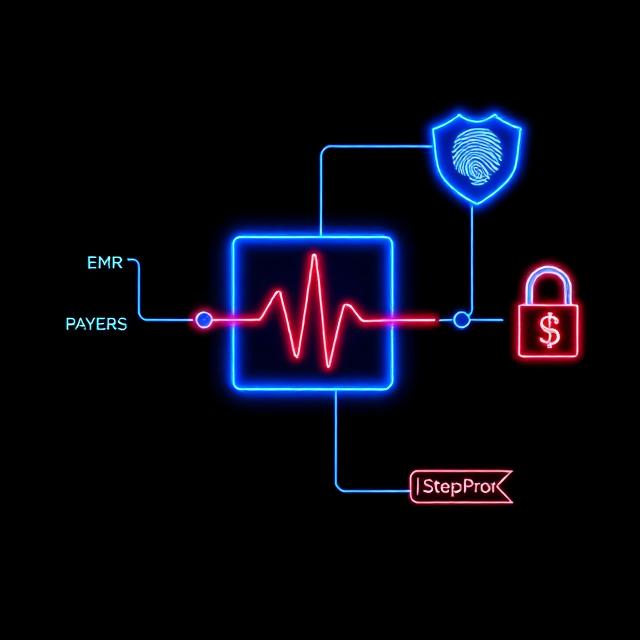
Verified actions for PHI workflows and clinical approvals.
Crittora applies Permission Gates, identity‑bound encryption, and Step‑Proofs to every PHI‑related action — across EMRs, labs, payers, and agents.
100%
HIPAA‑ready proof per approval
<1 MIN
to authorize or confirm access
100%
VERIFIED ACCESS TO EVERY ACTION<1 MIN
TO AUTHORIZE OR CONFIRM$0
UNTIL DOCUMENT IS VERIFIED (PASS‑THROUGH PRICING)<1 DAY
TO GO LIVE WITH Q.VerifyTL;DR
Crittora applies Permission Gates, identity‑bound encryption, and Step‑Proofs to every PHI‑related action — across EMRs, labs, payers, and agents.
Key Takeaways
- Crittora applies Permission Gates, identity‑bound encryption, and Step‑Proofs to every PHI‑related action — across EMRs, labs, payers, and agents.
- Audience: HIPAA‑Compliant File Exchange.
- Primary next step: Request a demo.
Quick Answers
What problem does this use case address?
Crittora applies Permission Gates, identity‑bound encryption, and Step‑Proofs to every PHI‑related action — across EMRs, labs, payers, and agents.
Who is this use case for?
HIPAA‑Compliant File Exchange
What should I do next?
Use the primary CTA: Request a demo.
The problems we solve in every handoff
PHI workflows fail when approvals are implied, integrations drift, or identity is weak. Crittora verifies identity, intent, and context before any action touches patient data.
Unauthorized Access & Approvals
Permission Gates ensure only verified clinicians and systems can authorize PHI actions.
Tampered Inputs & Integration Drift
Signed requests and sealed context detect replay or manipulation before execution.
Audit Failures & Regulatory Risk
Step‑Proof receipts provide cryptographic evidence for HIPAA and research audits.